Thank you so much @deano_ferrari for the hint into the right direction 
To quickly update the PCR policy of the sealed key, it was simply a matter of # fdectl tpm-authorize, as documented here.
$ sudo fdectl tpm-authorize
Signed PCR policy written to /boot/efi/EFI/OPENSUSE/sealed.tpm
Excluding PCR 10 from prediction (used by IMA)
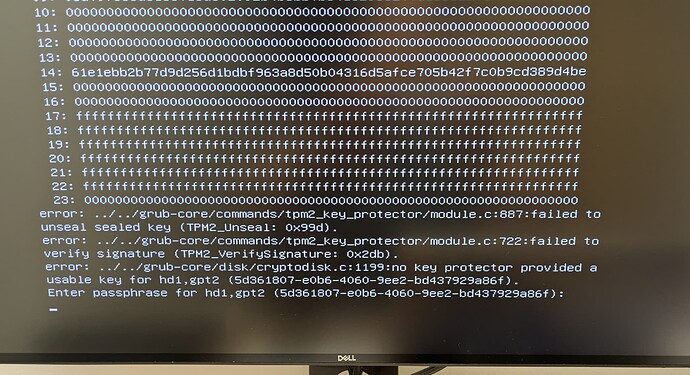
Although this fixed the TPM auto-unlock right away, there was still a silent issue remaining from the disk migration …
For the migration I have used a live USB, for which I temporarily disabled Secure Boot in the UEFI. After the auto-unlock did work again, I went into the UEFI to enable Secure Boot again, and I also enabled Fast Boot, which I was using previously too.
Unfortunately, this disabled the USB keyboard which prevented me from entering the UEFI setup during boot and from entering the LUKS passphrase in the GRUB2 bootloader, which was necessary again due to the changed UEFI settings …
As I did not have a PS/2 keyboard at hand, I did clear the CMOS of the motherboard with a jumper, which cleared firmware settings and TPM-related state.
At least, I could enter the encryption passphrase again afterwards and boot successfully into Leap 16.0.
In order to (re-)create the seal for the TPM2, I had to use the fdectl regenerate-key command, which did fail:
$ sudo fdectl regenerate-key
Device /dev/disk/by-id/nvme-nvme.<OLD-SSD>-part2 does not exist or access denied.
Authorized policy written to /etc/fde/authorized-policy/authorized-policy.tpm
Please enter LUKS recovery password:
Verifying LUKS recovery password (/dev/disk/by-id/nvme-nvme.<OLD-SSD>-part2)
Device /dev/disk/by-id/nvme-nvme.<OLD-SSD>-part2 does not exist or access denied.
Unable to open the device with the password
Error: Failed to verify password on LUKS partition (/dev/disk/by-id/nvme-nvme.<OLD-SSD>-part2)
After a while I noticed that fdectl is still trying to access the old NVMe SSD, which is not present anymore:
$ ls -l /dev/disk/by-id/nvme-nvme.*-part2
lrwxrwxrwx. 1 root root 15 Dec 28 12:53 /dev/disk/by-id/nvme-nvme.<NEW-SSD>-part2 -> ../../nvme0n1p2
Even specifying the correct mount path or device path with the --device argument to fdectl did not work …
Only afterwards I noticed that there is a configuration file for fdectl which is still pointing to the old NVMe SSD:
$ cat /etc/sysconfig/fde-tools
# Tunables for full disk encryption
# Configure whether to use old-style PCR policies, or TPMv2 authorized policies.
# Set to yes/no
FDE_USE_AUTHORIZED_POLICIES="yes"
# List of PCRs to seal the LUKS key to
FDE_SEAL_PCR_LIST="0,2,4,7,9"
FDE_SEAL_PCR_BANK="sha256"
# It appears that 128 is the maximum size of what TPM2_Load is willing to handle
FDE_KEY_SIZE_BYTES="128"
# These need to match exactly what grub2 uses to create the SRK
FDE_TPM2_SRK_ATTRS="userwithauth|restricted|decrypt|fixedtpm|fixedparent|noda|sensitivedataorigin"
# The PBKDF algorithm to use for deriving LUKS keys from a given password
# For grub2 based schemes, you have to use pbkdf2 for now.
FDE_LUKS_PBKDF="pbkdf2"
# Enable/disable tracing output
FDE_TRACING="true"
# This is used by the installer to inform "fdectl tpm-enable" about a key
# to enroll on the next reboot
FDE_ENROLL_NEW_KEY=""
# Specify the devices to be managed by fdectl
# NOTE: Those devices must use the same recovery password.
FDE_DEVS="/dev/disk/by-id/nvme-nvme.<OLD-SSD>-part2"
# [DEPRECATED] Use FDE_DEVS instead
# FDE_EXTRA_DEVS=""
# Configure whether to update the authorized policy in the sealed key after
# the bootloader update
# Set to yes/no
FDE_TPM_AUTO_UPDATE="yes"
# The RSA key size to be used for SRK and the private sign key
# Expected values: 2048, 3072, 4096, or just leave it empty to let fdectl
# to determine the size at runtime
FDE_RSA_KEY_SIZE=""
FDE_AUTHORIZED_POLICY="authorized-policy"
After changing the FDE_DEVS variable of this file, I could finally use the fdectl regenerate-key command to benefit from auto-unlock via TPM2 during boot again 
$ sudo fdectl regenerate-key
Authorized policy written to /etc/fde/authorized-policy/authorized-policy.tpm
Please enter LUKS recovery password:
Verifying LUKS recovery password (/dev/disk/by-id/nvme-nvme.<NEW-SSD>-part2)
Sealing secret - this may take a moment
Sealed secret written to /etc/fde/authorized-policy/sealed.tpm
copying /usr/share/efi/x86_64/grub.efi to /boot/efi/EFI/opensuse/grub.efi
BootCurrent: 0000
Timeout: 1 seconds
BootOrder: 0001
Boot0001 opensuse HD(1,GPT,<PARTUUID>,0x800,0x100000)/File(\EFI\OPENSUSE\GRUBX64.EFI)0000424f
BootCurrent: 0000
Timeout: 1 seconds
BootOrder: 0000,0001
Boot0001 opensuse HD(1,GPT,<PARTUUID>,0x800,0x100000)/File(\EFI\OPENSUSE\GRUBX64.EFI)0000424f
Boot0000* opensuse-secureboot HD(1,GPT,<PARTUUID>,0x800,0x100000)/File(\EFI\opensuse\shim.efi)
Unable to verify signature of a boot service; probably a driver residing in ROM.
Signed PCR policy written to /boot/efi/EFI/opensuse/sealed.tpm
Excluding PCR 10 from prediction (used by IMA)
Unable to verify signature of a boot service; probably a driver residing in ROM.
copying /usr/share/efi/x86_64/grub.efi to /boot/efi/EFI/opensuse/grub.efi
BootCurrent: 0000
Timeout: 1 seconds
BootOrder: 0001
Boot0001 opensuse HD(1,GPT,<PARTUUID>,0x800,0x100000)/File(\EFI\OPENSUSE\GRUBX64.EFI)0000424f
BootCurrent: 0000
Timeout: 1 seconds
BootOrder: 0000,0001
Boot0001 opensuse HD(1,GPT,<PARTUUID>,0x800,0x100000)/File(\EFI\OPENSUSE\GRUBX64.EFI)0000424f
Boot0000* opensuse-secureboot HD(1,GPT,<PARTUUID>,0x800,0x100000)/File(\EFI\opensuse\shim.efi)
Cheers Simon