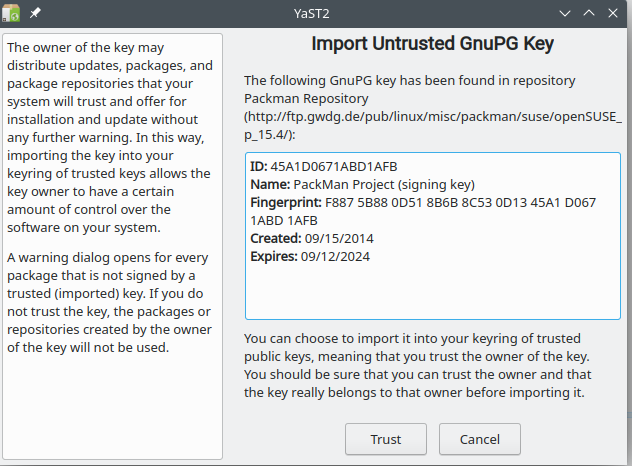
When I add the packaman package to the system a fingerprint is displayed. How can I verify the fingerprint is valid ?
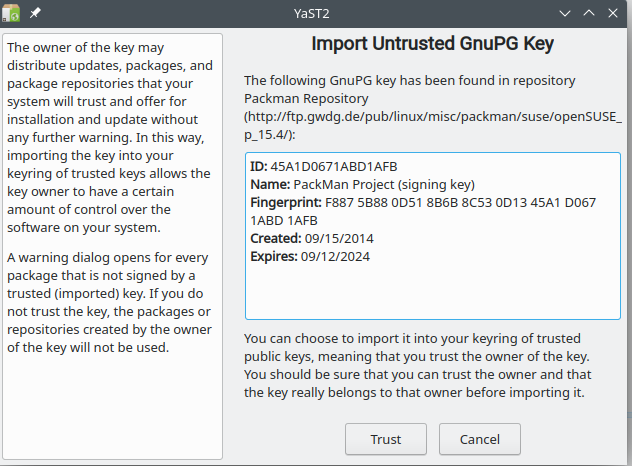
When I add the packaman package to the system a fingerprint is displayed. How can I verify the fingerprint is valid ?
You cannot. This is the weakest link of any public key cryptography. You can go to PackMan :: Documentation (links2linux.org), but you have no way to really trust that this site has not been impersonated. You can download key from keyservers and if it is signed by someone you trust, you have some more confidence in it. To the extent you trust the person who signed the key.
The install is asking me to trust the fingerprint. You must have a method to ensure the site can be trusted so users know that they can install packman repos otherwise what prevents impersonations ?
You could ask the same question about the openSUSE repos.
You aren’t asked about those, but only because the keys were automatically installed when you installed openSUSE.
In my case, I do have some SUSE and openSUSE keys in my gpg keyring. So I can use those to test the iso that I have downloaded. But when I originally added those keys to my keyring, I didn’t have much to go on.
As @arvidjaar said, that a problem with public key cryptography. It depends on trust, and there is no certain way to start that web of trust.
My web browser has some builtin keys for trusting sites. But can I be sure that I can trust my web browser? It’s the same problem everywhere.
These days, I just trust the packman key, because I recognize it from previous times.
If you want to be extra cautious, then:
Trust the key, but treat that as tentative;
disable the repo, so that you don’t actually use it for now;
wait a week or two. If the packman repo was hacked, you are likely to hear about it. If you don’t hear anything, the re-enable the repo and start using it.
This is not a perfect solution. But it’s about the best you can do.
I can verify the installation of Opensuse via SHA256 value the opensuse site provides so any apps or keys installed represent opensuse. Packman is a repos that Opensuse does not include in the O.S. and therefore if trusted I accept it not Opensuse.
That is the reason the message “import untrussted GnuPG key” appears. Does Opensuse provide verification for this key ?
Packman is not related in any way to openSUSE. So why should openSUSE provide verification for an external 3rd party repo?
arvidjaar already provided you the link to the packman site where you can find the key…
And by having a look there you can find additional infos…you just need to process this information:
http://wiki.links2linux.de/packman:faq_en
I understand that Packman is not related to Opensuse and that is my issue with accepting it for codecs. If Opensuse does not acknowledge Packman it is not trust worthy.
The link you provided is not https and although the title says wiki it is not the official wikipedia. openSUSE - Wikipedia. In the official Wiki I do not see any mention of Packman.
You seriously believe that https cannot be spoofed?
It seems you don’t even understand the differences…
Wikipedia openSUSE - Wikipedia (written by unknown guys and girls from the www)
openSUSE Wiki openSUSE Wiki (written by contributors, users and devs around openSUSE → this is the official openSUSE wiki!)
And in the official openSUSE wiki, Packman is described and mentioned several times if you use the search function: Search results for "packman" - openSUSE Wiki
And the link that i provided to you is the official Packman web presence.
A basic research will help a lot…
Give an example of where HTTPS is spoofed ? So all banking transactions can be compromised ?!!
I see the entry in Additional package repositories - openSUSE Wiki which is not a wiki but Opensuse wen site. They make a single refernce to packman but no confirmation of the expected fingerprint from the site there by validating the site.
For a fingerprint to be accepted there must be someone validating the fingerprint otherwise what is the point of showing the value? Since I cannot see any validating site for the fingerprint from Opensuse site it is not valid and I do not trust the site to accept repos information .
All that is needed is generating certificate “on the fly”. If it is signed by trusted root CA, you will not get any warning from browser. I doubt you examine every certificate chain on every SSL site you visit.
Whatever. You don’t understand and didn’t even read the provided information on the sites.
This is a list of currently existing third-party repositories , meaning they’re external to openSUSE. The packages in the below repositories are not supported by openSUSE, meaning they may not be tested . The repositories listed below can contain beta versions of software and other bleeding edge packages.
For new Linux and openSUSE users, it is recommended to use the four default repositories: OSS, Non-OSS, Update and Update-Non-OSS. Later on when you familiarize yourself with package management you can add more repositories, such as Packman.
You are contradicting yourself in many ways. You say you understand that packman is not related to openSUSE bur require a confirmation of openSUSE that packman is trustworthy…uhm no, this is not how it works…
When I read the Opensuse document site
in no way does it mention when installing Packman expect to see fingerprint F887 5B88 0D51 8B6B 8C53 0D13 45A1 D067 1ABD 1AFB. This is what makes Packman an Untrusted repository. To gain trust someone from Opensuse or another trusted source must acknowledge it is valid Fingerprint. Why else would they provide a fingerprint to look impressive? That is the point of this thread is determining trust for Packman.
I consider a valid Wiki to be from Wikipedia, the free encyclopedia from Wikipaadia the main online encylopeadia your domain for is https://en.opensuse.org. But thats fine I can refer to your wiki for Opensuse but I was unable to find any validation for the fingerprint. Why was a non https site given as a WIKI ?
Fair enough!
So to me this looks like you have to
Even simpler. since I already did a check and found no validating authorities.
I do not trust the packman repository and will not use it.
Your option but you will not be able to use propitiatory codecs for multimedia. sins openSUSE is open source only . Note the name,
That is fine. Trusting CODEC from a unproven repository is dangerous.
Did you have a look at the URLs in yast software for openSUSE repositories? They are all http. I wouldn’t trust them if i would be you… ![]()
![]()